With the ongoing threat of phishing attacks, spoofing, and other malicious activities, protecting your inbox and your identity online is crucial.
Domain-based Message Authentication, Reporting, and Conformance (DMARC) is a powerful email authentication protocol designed to give email domain owners the ability to prevent unauthorised use of their domains, commonly known as email spoofing.
These attacks can lead to serious consequences, including data breaches, financial fraud and the loss of sensitive personal or business information. DMARC works by aligning three key components – SPF (Sender Policy Framework), the message signature DKIM (DomainKeys Identified Mail), and the “From” header through the DNS of a domain.
Below, we explore what DMARC is, break down its components, explain its purpose and benefits, and dive into how it works.
Note: You can protect your domain, secure your brand and take control of your email by using our free DMARC wizard tool.
What are the benefits of using a DMARC?
Stops Spoofing – Prevents unauthorised use of your domain in email headers, thus reducing phishing risk.
Improves Email Deliverability – ISPs trust DMARC-protected domains more, improving the deliverability of mail.
Increases Visibility – Aggregate reports help monitor who is sending emails on your behalf.
Protects Brand Reputation – Customers trust your brand when they know their inbox is protected.
Aligns with Compliance – Many industries (e.g. finance, healthcare) require or recommend DMARC for email security compliance.
Reporting mechanism, the domain owner can see exactly who is sending emails from their domain, how all mail is handled and when.
What are SPF and DKIM records?
SPF (Sender Policy Framework)
An SPF record is a type of DNS record that dictates which IP addresses or hostnames are authorised to send mail for the domain.
This record greatly reduces the risk of your domain being spoofed and it can also improve deliverability to stricter mail providers, such as Outlook and Gmail.
ℹ️ How to add an SPF record on our platform: https://docs.20i.com/email-hosting/spf-records
DKIM (DomainKeys Identified Mail)
DKIM, like SPF, is a type of DNS record that enables a specific aspect of email-sending processes to be authenticated.
This record will provide a foundation for distinguishing legitimate mail by placing a DKIM signature in the headers sent from the mail server.
The receiving server will then extract the DKIM signature from the mail header, fetch the DKIM record from the domain’s DNS and then validate the message using the 2048-bit public key from the DKIM DNS entry.
ℹ️ How to add a DKIM record on our platform: https://docs.20i.com/domain-names/add-dkim
DMARC Record Structure
A DMARC record is a DNS TXT record published at _dmarc.yourdomain.com.
Here’s an example record and what each part means:
v=DMARC1; p=reject; rua=mailto:dmarc-reports@yourdomain.com; ruf=mailto:forensic@yourdomain.com; pct=100; sp=quarantine; adkim=s; aspf=s
DMARC Tag Breakdown
v=DMARC1 – Version
- Required: Yes
- Purpose: Indicates the DMARC protocol version. Currently, this is always DMARC1.
- Details: Must be the first tag in the record.
- Example: v=DMARC1;
p – Policy
- Required: Yes
- Purpose: Specifies the policy for how to handle messages that fail both SPF and DKIM alignment checks.
- Options:
- none: No action taken, just report (useful for just monitoring).
- quarantine: Mark the message as suspicious (e.g., place in spam/junk).
- reject: Block the message outright.
- Best Practice: Start with none, evaluate reports, then move to quarantine, and eventually reject.
- Example: p=reject;
rua – Aggregate Reports URI
- Required: No
- Purpose: Tells recipients where to send aggregate reports (in XML format). These are daily summaries showing sources and authentication results.
- Format: mailto:your-email@example.com
- Multiple recipients: Separate with commas.
- Privacy Note: Consider using a dedicated mailbox for reports.
- Example: rua=mailto:dmarc-reports@example.com;
ruf – Forensic (Failure) Reports URI
- Required: No
- Purpose: Sends detailed failure reports (for individual failing messages).
- Format: Same as rua, but usually under more strict privacy rules.
- Usage Warning: These can contain full message content (Personally Identifiable Information risk), and many providers no longer send them.
- Example: ruf=mailto:forensics@example.com;
pct – Percentage
- Required: No
- Purpose: Applies the policy (p) to only a percentage of messages.
- Range: 1–100
- Use Case: Great for gradual rollout of quarantine or reject.
- Example: pct=50; (Applies to 50% of failing messages)
sp – Subdomain Policy
- Required: No
- Purpose: Sets a different policy for email from subdomains (like mail.sub.example.com) than the main domain.
- Options: none, quarantine, reject
- Defaults to: The main p policy if omitted.
- Example: sp=quarantine;
adkim – DKIM Alignment Mode
- Required: No (defaults to r if not specified)
- Purpose: Controls how strictly the DKIM domain must match the “From” domain.
- Options:
- r (relaxed): DKIM domain must be a subdomain of the From domain.
- s (strict): Must be an exact match.
- Use Case: Use s for tight control; r if you use third-party senders like Mailchimp.
- Example: adkim=s;
aspf – SPF Alignment Mode
- Required: No (defaults to r)
- Purpose: Controls how strictly the SPF domain must match the “From” domain.
- Options:
- r (relaxed): SPF domain can be a subdomain.
- s (strict): SPF domain must be an exact match.
- Tip: Use r if you have external senders (e.g., CRMs, cloud services).
- Example: aspf=r;
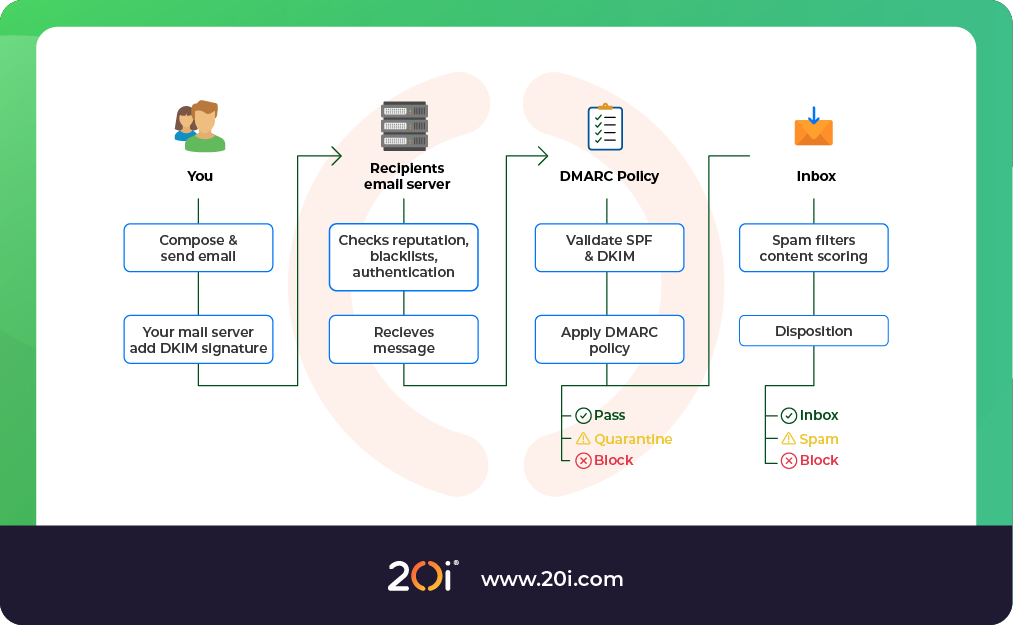
How does DMARC work?
Here is a simplified version of what happens when a DMARC-enabled domain sends an email:
- Sender sends an email from yourdomain.com.
- Receiving server checks DNS for DMARC policy at _dmarc.yourdomain.com.
- It then validates, depending on what it set out within the record
- SPF: Does the IP/hostname match a server in the domain’s SPF record?
- DKIM: Is there a valid DKIM signature aligned with the domain?
- Alignment check: Are the domains in the “From” header aligned with the SPF/DKIM domains?
Based on the result:
If both SPF and DKIM fail, the DMARC policy is applied (none, quarantine, or reject).
The receiving server optionally sends a report (RUA or RUF) to the domain owner.
Sample DMARC Records for Different Scenarios
1. Monitoring Only
v=DMARC1; p=none; rua=mailto:dmarc-reports@example.com;
2. Aggressive Enforcement
v=DMARC1; p=reject; rua=mailto:dmarc-reports@example.com; ruf=mailto:failures@example.com; adkim=s; aspf=s; pct=100;
3. Testing Quarantine on 25% of Failures
v=DMARC1; p=quarantine; pct=25; rua=mailto:dmarc-reports@example.com;
How to implement DMARC
Implementing a DMARC will vary depending on your hosting, internet or mail provider, however, the records themselves are typically universal.
If you are unsure of how to apply a DMARC to your domain, it is best to contact your provider.
ℹ️ If you’re hosted with us, simply use our free and easy DMARC Wizard. Learn how to implement a DMARC here https://docs.20i.com/domain-names/how-to-use-the-dmarc-wizard-tool.
Final Thoughts
With cyber threats more prevalent than ever, DMARC is a must-have for email security.
It puts the control in your hands, telling inbox providers what’s legitimate and what’s not, while giving you the visibility to manage your domain’s email health.
At 20i, we don’t believe that you should have to pay extra for security features, so we include an extensive security suite with our Reseller Hosting and Managed Cloud Servers.
As a reseller, this is something that you can advertise as your own and provide to your customers for free to distinguish yourself from mediocre hosting providers.