StackProtect is a security tool from 20i that protects website passwords.
One of the most common and easy ways to compromise a website is to guess the password for login to its content management system (CMS). For example, /wp-admin for WordPress.
Malware will use trial-and-error to try to guess your password.
It might start by cycling through variants of the most common passwords. This is known as a dictionary attack: where the code cycles through all the words in a ‘password dictionary’, using common words and passwords that have been used already elsewhere.
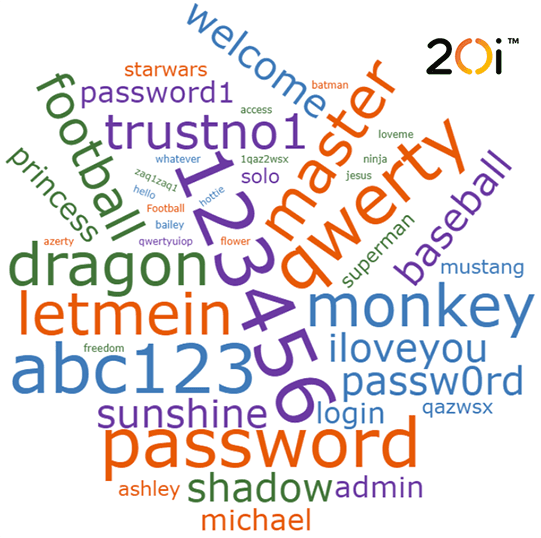
It’s why it’s you should use a unique, secure password: one that is truly random. This makes them difficult to remember – unfortunately – but there are password managers that can help with this.
Then there is the traditional brute force attack, where the code tries every character combination in sequence. Even if your password is random, these types of attacks stand a good chance of guessing it right, given time.
How StackProtect protects your password
StackProtect monitors requests to common login pages. When a request is made, it looks at a number of things:
- Publicly blacklisted domains and IPs
- Unusual geographic location (from the IP address)
- Previous login attempts from that host
- Number of login attempts, and how many websites they’ve tried to access
- Failed logins and previous firewall rule breaking
We’ll apply Google’s latest reCAPTCHA tests If these criteria are matched. In most cases, this provides a decision as to whether to allow a login or not. For brute force attacks, they will be stopped.
In the rare cases where Google’s tools can’t make a decision, the user will be presented with a traditional CAPTCHA box like this:
The splash page is served before any of the CMS’s code is executed. It takes place on physically isolated servers, so that malware can’t access the core data for your site.
This combination of our checks and Google’s checks stop the brute force script in its tracks.
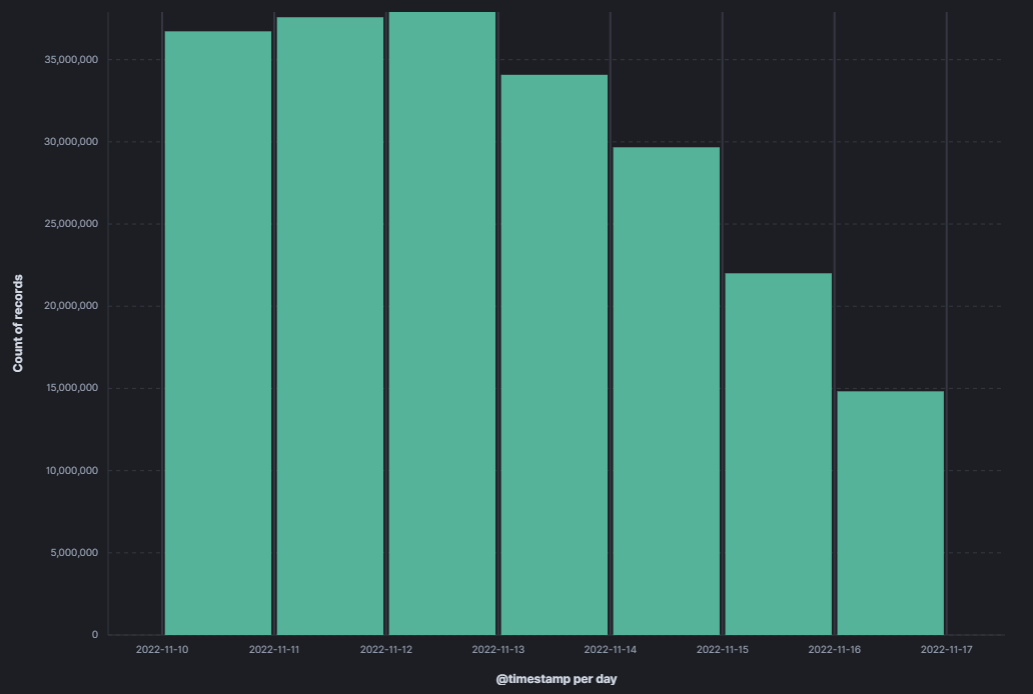
Brute force attacks happen very, very often. For example, in November 2022 we had between 15 and 37 MILLION attacks every day!
It’s just one of the ways that we help keep you secure.
Sadly, there are data breaches every day and no one can promise to keep you 100% secure. Even so, there are plenty of other ways that you can limit your exposure to harm from cyber criminals. We recommend using multi-factor authentication, physical security tokens and/or biometric methods (like fingerprints and retina scans) where possible.
Protecting your passwords is an important part of cyber security, but it’s also important to ensure your site is secure. Read our comprehensive WordPress Security Guide to find out more about how you can prevent and reduce the threat of hackers.
