SECURE HOSTING
Enterprise level website security built-in
Security breaches and exposure to malware are an ever-present threat on today’s web. Our secure UK hosting keeps you safe against harmful web attacks. We give you the tools to help you save time, money and your reputation. We don’t think that you should be charged for these services.
Stay a step ahead of online criminals with 20i, at no extra cost.
Breadcrumb Navigation
FREE AND ON-DEMAND
Automatic malware scanning
We scan all websites every day for common malware. Using commercial tools and systems developed in-house, we discover all sorts of nasties. Malware – such as web shells or mail/spam daemons – can compromise your installation, giving criminals access to your site’s data, email and content.
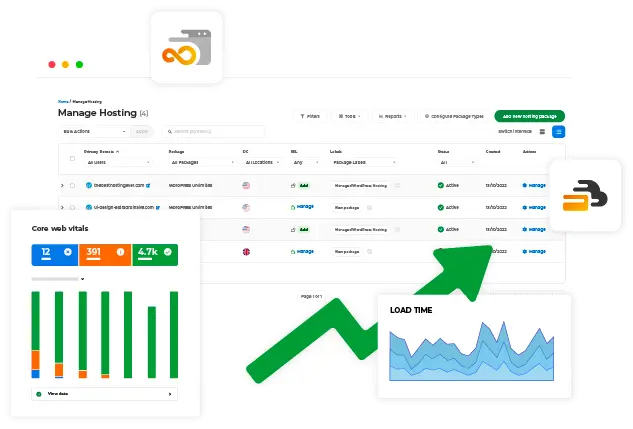
We give you a detailed report on the results of this scan in our My20i control panel. This is similar to services provided by some other web hosts – which they charge a premium for!
Should malware be discovered, we can send you an email alert.
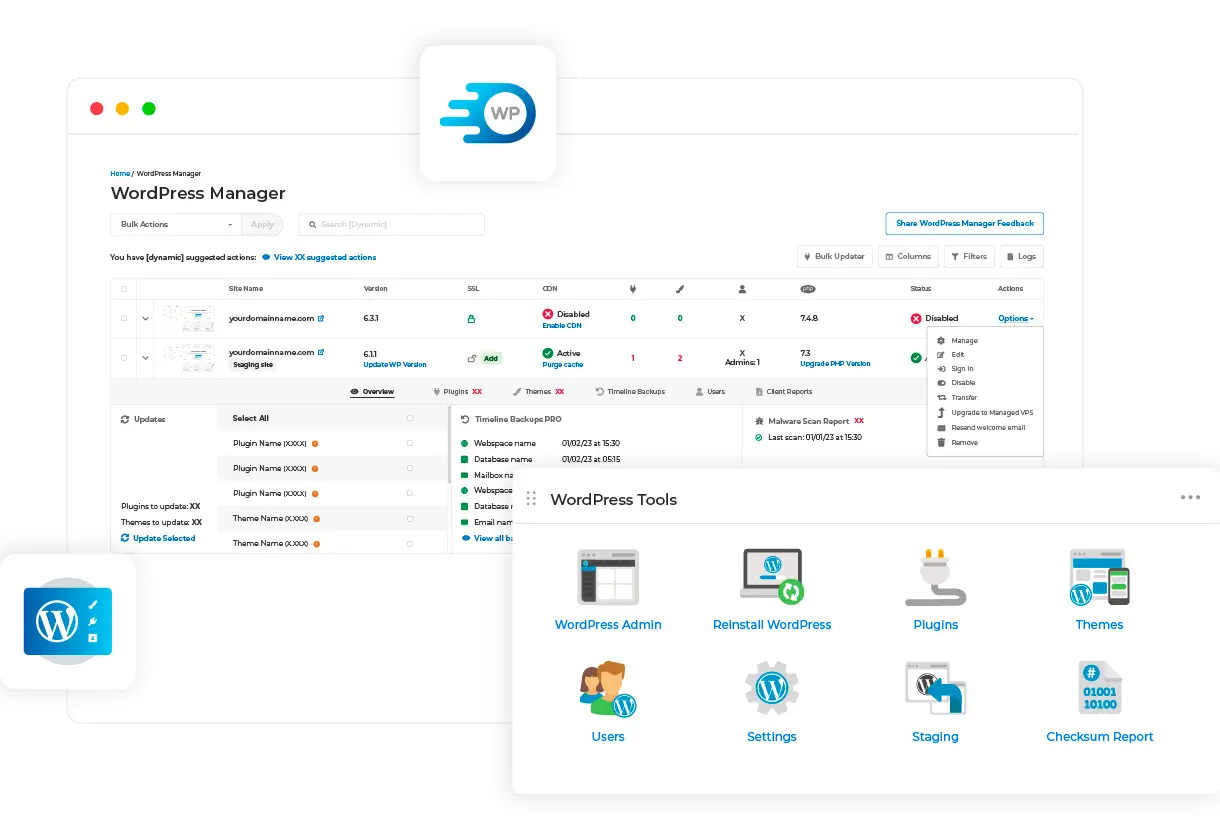
WordPress users also have another way to check for malware, through our WordPress Checksum Report in our WordPress Tools suite. This checks that your WordPress core matches the official WordPress repository.

Immediate results
If you’ve discovered malware on your site, you’ll need to update the software or plugins, and delete any compromised files. Once you’ve made the changes, you can re-scan right away. You’ll get confirmation on whether your fixes have worked immediately.
On-demand scanning
What makes our malware scanning special is that you can also run our scanner on-demand. This is convenient because you don’t have to wait until the next scheduled scan.
Disables PHP Mail
If malware is detected, PHP mail is disabled to prevent your site from further infecting others through email.

HTTPS EVERYWHERE
Free wildcard SSL encryption
SSL-TLS certificates are an integral part of secure web browsing and data transfer. Legal regulations and promotion by Google have made it essential that every site should have one. So we partner with Let’s Encrypt to make every site we host an ‘https’ one.
Our free SSLs are ‘wildcard’ certificates. So you can secure subdomains as well as your primary domain using one certificate. To get a free ‘https’ certificate your site needs to use the validated 20i nameservers. They provide the same level of security as any other SSL certificate.
BUILT FOR BUSINESS
Our data centres
Strict security policies are in place at all of our data centres, including:
- 24-7 security on site
- Photo ID and swipe card entry
- CCTV inside and out
- Gated access and secure perimeter fencing
- Redundant and uninterruptible power supplies
20i employees need to identify themselves before accessing any internal system. We use centralised identification and security policies that follow a least-privilege and need-to-know access policy.




Security credentials
We hold industry-recognised security certifications and accreditations, including ISO 9001, ISO 22300, ISO 27001 and SOC2 Type 2. Click here for more information.
Isolated backups
We rigorously follow the 3-2-1 rule, and that starts with our Database, Web, FTP and Mail servers operating as completely separate stacks, each with local redundant backups ready to take over in an instant.
We use a different datacentre for our fully offsite backups to ensure true disaster recovery protection is in place.

EMAIL SCANS
Anti-spam, anti-virus
All emails and forwarders sent and received are subject to advanced antivirus and anti-spam protection.
We use 3 layers of inbound spam and virus scanning:
Network-level
Commercial anti-spam deny lists from Spamhaus, Invaluement and Barracuda Networks are used to reject mail from known spam networks.
Virus Scanning
Any known malware signatures are rejected.
Content-based
Messages are scanned for spam-like characteristics and filtered into the ‘junk mail’ folder.


Fully configurable email filters
These filters are fully configurable via the webmail control panel. So certain senders, domains and TLDs can be allow-listed to bypass the content filter entirely. The same goes with deny lists: you can create your own from our control panel.
Whenever we reject a message for a known virus or network deny listing, the message is returned to the sender so the sender knows what's happening. We never ‘black hole’ email.

Spammers not welcome
If you’re using the email accounts included with our shared hosting, you don’t want miscreants to harm your reputation (and ours) by sending out masses of ‘spam’ email.
So we monitor outgoing emails to ensure this doesn’t happen and operate a zero-tolerance spam policy.
CYBER ESSENTIALS ACCREDITED
Third-party verified secure hosting

We’re proud to have achieved Cyber Essentials accreditation. This annually renewed, government-backed scheme demonstrates our ongoing commitment to robust cybersecurity practices.
This certification ensures that we’ve implemented stringent measures to protect your website and data against threats, and verified that our network, including internet gateways and servers, meets strict security standards.
Whether you’re running a personal blog, a small business site or a large e-commerce platform, you can be confident that we will safeguard your data, reputation and customer information.
Just like our other security features, this comes at no extra cost to you – it’s all part of our mission to keep your online presence safe and secure.
20i has earned the Secure Hosting Alliance’s (SHA) Trust Seal. This certification shows that 20i is committed to the highest standards of security, reliability and customer protection.
20i is part of the initial group of responsible hosting providers whose business practices reflect a strong customer orientation and provide a high level of trust and security.
TWO-FACTOR AUTHENTICATION
Safer than just a password

Unfortunately many security measures are rendered ineffective if your password is compromised. So we offer the option to use two-factor authentication (2FA) for My20i, StackCP and SSH access.
2FA is a way to add an extra layer of security. Our 2FA uses TOTP apps, which provide you with a time-sensitive single-use code to enter as well your password. 2FA app providers include Google and Microsoft. The apps are run from your phone.
We also enforce another form of ‘2FA’: random security checks when payments are made. This will require you to call us and confirm additional security information provided by yourself when first signing-up.


1 TBPS+ ANTI-DDOS
Enterprise-level denial of service protection

Distributed denial of service (DDoS) attacks are a growing hazard on the web. They can do extensive damage to a business by flooding the server with requests, so that regular website users are unable to access your website.
If your shared hosting or virtual private server (VPS) is attacked, usually you don’t have much of a choice other than to weather the storm and wait for the attack to stop.
That’s why we introduced 1 Tbps+ anti-DDoS protection. This enterprise-level protection covers you against most attacks. It only filters-out malicious traffic, so you can carry on working without noticing any interruption. Don’t let the hackers ruin your business.
WEB APPLICATION FIREWALL
Strong external protections
One way to stop security breaches is to prevent criminals getting access to your code on the server. Our Web Application Firewall (WAF) protects your data and software by blocking suspicious activity.
A common attack on a website is to use web forms to insert malicious code. Forms aren’t covered by traditional firewalls, as they need to allow information to pass from the user to the server where the website is hosted. They can be an access point for data thieves or ransomware.
Even in the best-case scenario, being a victim of this will cost your business time and money. Worst case: a breach could end your company.
The 20i WAF helps prevent this by inspecting every HTTP request for SQL injection, trojans, cross-site scripting, path traversal and many other types of attack. It does this at the edge our network, so it happens before any scripts from web apps like WordPress execute. It takes less than a millisecond.
The 20i security team regularly update the set of rules that filter-out malicious requests. This ruleset is made from commercially-available resources and custom rules written by the 20i security team.
All this makes it much more difficult to hack your sites, and goes on behind the scenes at 20i.


NETWORK PROTECTIONS
Keeping attackers away from your web apps

As well as the firewall, we also operate network defences. These are based on IP address and network-level (automated system) level reputation. They’re designed to block likely attackers before an attack starts.
Suspicious IP addresses and networks are routed to different web servers automatically, so traffic and load is kept away from standard web servers. IP addresses that have a bad reputation are blocked at the network edge, and entire ranges of IP addresses can be blocked too.
STACK PROTECT
Brute-force login protection

A common attack vector for cyber criminals is to use brute force to guess your website’s ‘admin’ password. These are applications that cycle through common passwords and use trial and error – random letters and numbers – to try to crack your credentials.
Our platform includes StackProtect, which monitors log-in attempts to your website. It checks for potential ‘evil’ automated requests. If they’re detected, it uses Google’s latest reCAPTCHA tools and if necessary, blocks those attempts.
This also stops our platform being slowed-down. It blocks up to six million requests – every day. Logins to our WordPress hosting platform are our most popular target, but StackProtect covers all common website logins.

INFRASTRUCTURE THAT’S UNMATCHED FOR RESILIENCE
The best platform for security
The unique ways we set up our servers makes huge differences.

Autoscaling
A cyber-attack uses up a lot of web hosting resources, even if it’s unsuccessful. If you’re on our shared hosting, our autoscaling servers will account for the attack, meaning that your site will stay fast and online. At other hosts, an attack on one of your hosting ‘neighbours’ can slow down your site. Not so at 20i.

No single point of failure
Our platform has redundancy at every level. In the event of a hardware, software or network failure, automatic failover occurs to bring services back online. This redundant hardware and software design helps availability and mitigate data loss.

Isolated server roles
Web servers serve only websites, MySQL servers just run MySQL and email servers only email. Logs are sent to central log servers. These isolated server roles mean that even in the worst-case scenario where your website was compromised, an attacker won’t be able to cover their tracks or read your email.
SELF-MANAGED SECURITY
Lock down your website

Block visitors to your site IP address or country
Our hosting allows you block malicious IP addresses, entire subnets or even whole countries, if you like. That’s up to you.

Website password manager
You can add passwords to areas of websites or whole sites quickly and easily, without having to code.

File transfer denied
Commonly used access systems such as FTP, SFTP, Remote MySQL and SSH are denied as standard and can only be enabled after authentication through the control panel. You can unlock FTP for a set period of time so you can make changes, then it will lock automatically.

File permissions checker
Scan your website files for permission-based errors to prevent unauthorised access. Our File Permissions Checker will recommend and fix errors automatically.

Backups
If the worst happens, you should still have website backups to fall back on. You can create site backups quickly and easily in our control panel or set them to happen automatically.

Password generator
Generate secure random passwords from within our control panel. No need to resort to external password creation applications.

Secured by TLS
FTP and SFTP is secured by Transport Layer Security protocols: the same crypto that helps create ‘https’ URLs. So, file transfers are less likely to be read or tampered-with by criminals.

CDN security headers
Manage all of your website’s HTTP security headers in a simple dashboard. You can toggle the policies that allow or deny the passing-on of security-related information between the client and server.
Low prices

Reseller Hosting
£1 first month

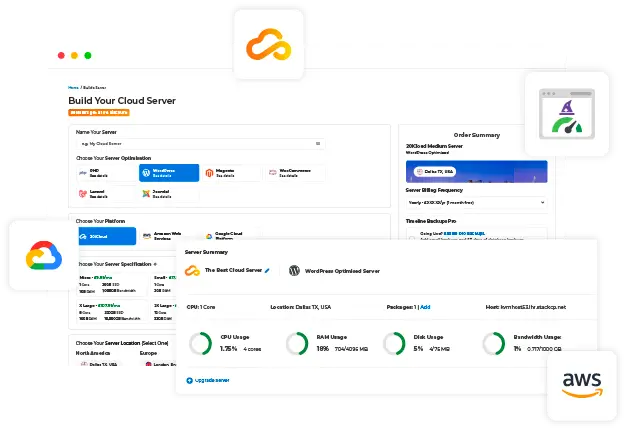
Managed Cloud Servers
From £9.99 /month

Managed WordPress Hosting
£1 first month

Managed Laravel Hosting
£1 first month

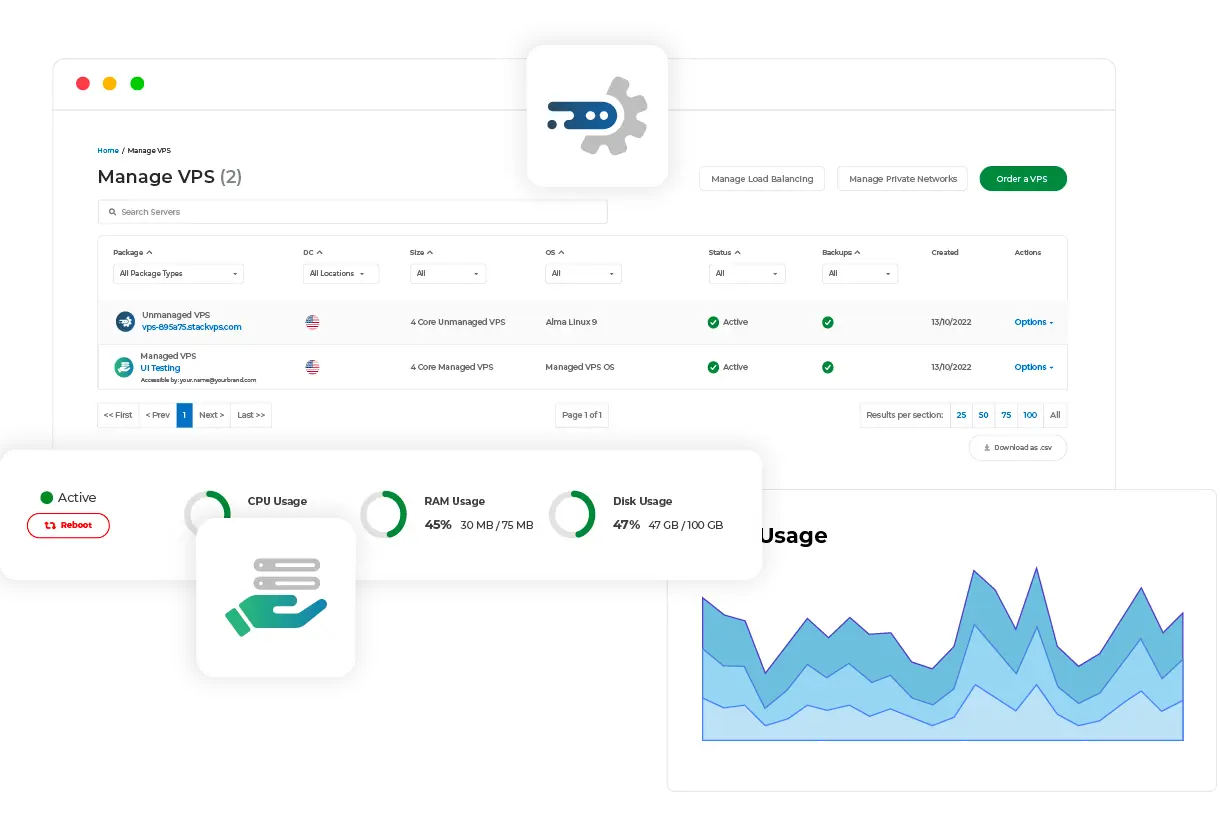
Virtual Private Servers
From £9.99 /month